
Google Sync Integration
Guide
VMware Workspace ONE UEM
Integrate your Google Sync
Infrastructure using Workspace
ONE UEM
1
Organizations using the Gmail infrastructure may be familiar with the challenge of securing email
endpoints for Gmail and preventing mail from circumventing the secure endpoint. Workspace
ONE UEM provides you with an end-to-end solution that enables you to fully integrate your Gmail
infrastructure without compromising security.
Integrating your Gmail infrastructure with Workspace ONE provides the following benefits:
n Flexible configuration while maintaining tight integration
n Email monitoring and management
n Customizable access control
n Google Sync support
For more information on Google Sync, see https://support.google.com/a/answer/135937?hl=en.
Understanding Google Sync Integration Methods
Integrate Google Sync infrastructure using the Workspace ONE UEM end-to-end solution to
securely integrate, access, and manage your email.
To suit your business needs, you can integrate Google Sync in different ways by using the
different deployment models offered by Workspace ONE UEM. The integration methods you
choose require configuring of certain settings on the UEM console. To know more about
these integration methods, see Chapter 2 Deployment Methods to Integrate your Google Sync
Infrastructure topic.
Google Sync Setup
To start managing your Google users with Workspace ONE UEM, you also require Google
specific settings and permissions. To know how to set up these permissions and enable settings,
see Chapter 3 Create an Admin Role for Gmail Integration.
VMware, Inc.
4

Manage Devices
To effectively monitor and manage your devices, you can use the Email Compliance Policies,
Email Dashboard, and the List View page on the UEM console . Not all the email policies and the
actions performed from the dashboard are applicable for all the integration methods. To know
the applicable email policies and dashboard actions, see the Chapter 2 Deployment Methods to
Integrate your Google Sync Infrastructure.
Requirements for Google Sync Deployment
You must fulfill the Workspace ONE UEM requirements in order to successfully integrate your
Gmail infrastructure with VMware Workspace ONE UEM.
Note Disclaimer - Integration with third party products is not guaranteed and dependent upon
the proper functioning of those third party solutions.
n Google admin account with Super Admin permissions.
n API Access to Gmail.
n End users must accept the Google end-user license agreement.
Note The Gmail provisioning API version 2.0 and the new Directory API are not FIPS compliant.
Google Sync Integration Guide
VMware, Inc. 5
Deployment Methods to Integrate
your Google Sync Infrastructure
2
Workspace ONE UEM offers different deployment models to integrate Google Sync for your
organization.
Types of Integration
Depending on the deployment method you choose, the Workspace ONE UEM server
communicates with the Gmail server one of the following ways:
n Proxy deployment - The Workspace ONE UEM server communicates indirectly with the
Google server through Secure Email Gateway(SEG.)
n Direct deployment - The Workspace ONE UEM server uses the Google directory APIs or the
password management configurations.
SEG Proxy Integration With and Without Password Management
SEG V2 supports this configuration. This configuration type involves the SEG Proxy server
residing between the Workspace ONE UEM server and the Gmail server. The SEG Proxy server
ensures security by not allowing the enrolled devices to communicate directly with the Gmail
server. With SEG, you get visibility of both the managed and unmanaged devices on the Email
Dashboard. You can also leverage the available email policies.
Direct Integration with Directory APIs
In this configuration type, the Workspace ONE UEM server uses Google's directory APIs to
manage email access on mobile devices.
Direct Integration using Password Management
VMware, Inc.
6
Using the password provisioning configuration type, the Workspace ONE UEM server
communicates directly with Google. Since the SEG server is not involved, this configuration
uses password switching to block non-compliant devices. Based on your security needs, you
may either choose to store or purge the password in your database. There are two types of
configuration available:
n Integrating with password retention - Using this configuration, the Workspace ONE UEM
server communicates with the Google server directly and retains the Google password in
the database by default. You can manage and monitor enrolled devices through the Email
Dashboard. Devices are deemed compliant or non-compliant based on the email compliance
policies configured within the Workspace ONE UEM console console .
Whenever a device is non-compliant, Workspace ONE UEM resets the password on the
Google server preventing the user to log in using another device. Once the device is back to
compliant status, the old password is reset back on the Google server and the user can gain
access using the old password. By default, unmanaged devices are blocked.
n Integrating without password retention: VMware Workspace ONE UEM recommends using
this configuration. Using this configuration, the Workspace ONE UEM server communicates
with Google directly and does not store the user password in database. You can manage and
monitor enrolled devices through the Device Dashboard. Devices are deemed compliant or
non-compliant based on the device compliance policies configured within the
UEM console .
Since the SEG server is not involved, this approach provides a way to block non-compliant
devices and ensure password safety. Once a device is detected as non-compliant,
Workspace ONE UEM removes the email profile from the device, thus barring the user
from receiving emails. Once the device is back to compliant status, Workspace ONE UEM
generates a new password and sends it to Google and onto the device through the email
profile.
Configure Secure Email Gateway V2 With Workspace ONE
UEM console
Integrating SEG (V2) Proxy with Google is a two-step process.
You must first configure the SEG (V2) Proxy using the UEM Console and then configure the IP
restriction on the Google admin console.
Configure the various SEG (V2) settings such as email, external and server settings, and security
information.
Prerequisites
You must have downloaded the SEG server SSL certificate.
Google Sync Integration Guide
VMware, Inc. 7

Procedure
1 Navigate to Email > Email Settings. The Configuration wizard
displays.
2 Click Configure.
a From Deployment Model, select Proxy.
b From Gateway Platform, select V2.
c From Email Type, select Google and then select Next.The Deployment tab opens and
displays the basic settings.
3 Select the Friendly Name text box and enter a unique name.
4 Configure the External Settings. Select the External URL and Port text box and enter the
external URL and the port number to which Workspace ONE sends policy updates.The
supported format is https://<external seg url>:<external port>.
5 Configure the Server Settings.
a Enter the web listener port for SEG . By default, the port number is 443. If SSL is enabled
for SEG, the SSL certificate is bound to this port.
b (Optional): From Terminate SSL on SEG, select Enable to bind the SSL certificate to the
port.
c Select Upload Locally to upload the SSL certificate during installation. Use this setting
when you do not have the certificate during MEM configuration. See, Configure the SEG
V2 section in the Secure Email Gateway (SEG) V2 guide.The UEM console supports
uploading the certificate locally for easy OTA installation. The certificate can also be
provided during run-time.
d From SEG Server SSL Certificate, select Upload to add the certificate.The SSL certificate
can be installed automatically, instead of providing it locally. This setting is useful for
larger SEG deployments. An SSL certificate in the .pfx format with full certificate chain and
private key included must be uploaded. See, Configure the SEG V2 section in the Secure
Email Gateway (SEG) V2 guide.
6 Configure the Email Server Settings. Select Email Server URL and Port and enter the Google
server URL: https://m.google.com.This is the Google address to which the SEG will proxy
ActiveSync requests.
Google Sync Integration Guide
VMware, Inc. 8

7 Configure Security Settings.
a From Ignore SSL Errors between SEG and email server, select Enable to ignore the
Secure Socket Layer (SSL) certificate errors between the email server and SEG server.
b From Ignore SSL Errors between SEG and Workspace ONE UEM server, select Enable
to ignore Secure Socket Layer (SSL) certificate errors between the Workspace ONE UEM
server and SEG server.Establish a strong SSL trust between Workspace ONE UEM and
SEG server using valid certificates.
c From Allow email flow if no policies are present on SEG , select Enable to allow the email
traffic if SEG is unable to load the device policies from the Workspace ONE UEM APIs.By
default, SEG blocks email requests if no policies are locally present.
8 Configure Cluster Settings. From Enable Clustering, select Enable if you want to enable
clustering of SEG servers. For more information, see Configure the V2 Platform section of
the VMware Secure Email Gateway guide.
9 (Optional): Configure the Automatic Password Provision setting in Google Apps. Skip this
step if you provide the Google password to your device users or if they are provided with
their SSO password that is the same as the Google password.The
Automatic Password
Provision setting is deactivated by default because it is considered to be more stable when
the Google password is managed within your organization.
a If you do not provide native passwords to device users, or if they are only provided with
SSO password and the primary directory is not Google, select Enabled.When enabled,
the UEM console provisions the Google for your users.
b Enter the following information for the UEM console to provision the Google password:
Setting
Description
Google Apps Domain Google Apps domain address.
Google Apps Sub-Domain Google Apps sub-domain address.
Google Apps admin username Complete URL as the Google Apps Admin user name.
Service account certificate Click Upload to upload to the Service account certificate. Enter the
certificate password when prompted. The certificate password is created
when generating the client ID on the Google console.
Directory service account email
address
Directory service account email address that is generated while creating
the Service Account Certificate.
Application Name Specify the project name created earlier.
Google User Email Address Certificate attribute which holds the email address of the user.
10 Enter the required settings in the Profiles tab and click Next.
For more information on the settings in the Profiles tab, see the Configure the V2 Platform
section of the VMware Secure Email Gateway guide.
11 Click Finish.
Google Sync Integration Guide
VMware, Inc. 9

What to do next
Configure IP Restriction on the Google Admin Console to complete the integration of SEG (V2)
proxy with Google.
Configure Advanced Settings
Configure advanced settings to complete the process of integrating SEG Proxy with Google
Sync.
Prerequisites
Complete the SEG Proxy settings configuration before configuring the advanced settings.
Procedure
1 Navigate to Email > Email Settings page and then select the icon next to the required Google
Sync deployment.
Note By default, the Use Recommended Settings check box is enabled to capture all SEG
traffic information from devices. If not enabled, you can specify what information and how
frequently the SEG should log for devices.
2 Select the Enable Real-time Compliance Sync option to enable the UEM console to remotely
provision compliance policies to the SEG Proxy server.
3 Click Save.
Configure IP Restriction on Google Admin Console
Configure Google Sync to accept traffic only from SEG. This restricts the communication to SEG
and ensures that the devices that attempt to bypass SEG are blocked.
Prerequisites
Google Sync Integration Guide
VMware, Inc. 10

You must have configured SEG V2 settings on the UEM console.
Procedure
1 Log into the Google Admin console and navigate to
Devices > Mobile and endpoints > Universal settings > Data Access > Google Sync
Sync.
.
2
Select the Google Sync IP Whitelist text box and enter the external SEG IPs that you want to
allowlist.
3 Click Save.
Integrate Direct Model using Password Management
While configuring your Gmail deployment using the Password Management approach, you can
choose to retain or not retain the Google password in the Workspace ONE database.
Google Sync Integration Guide
VMware, Inc. 11

The non-compliant devices are blocked depending on whether you chose to retain the password
or not. The devices are blocked either by resetting the password on the Google server or by
removing the email profile from the device.
Note Irrespective of the type of email client, for password provisioning to occur, all the Gmail
models require an EAS profile. For new installs, associating an EAS profile is mandatory. For the
upgrades, the admin has to manually associate an EAS profile to the MEM configuration after
completing the upgrade process.
Procedure
1 From the UEM console main menu, navigate to Email > Email Settings, and then click
Configure.
2 Set these requirements in the Platform wizard form.
a Select Direct as the Deployment Model.
b Select Google Apps using Password Provisioning as the Email Type.
c Select With Password Retention or Without Password Retention as the Google
Deployment Type.
d Select Next.
3 In the Deployment wizard form, complete the following options.
Setting
Description
Friendly Name Enter a friendly name for the Gmail deployment.
Google Apps Domain Enter the registered Google Apps domain address.
Google Apps Sub-Domain Enter the Google Apps sub domain address, if applicable.
Google Apps Admin Username Enter the full email address in the Google Apps Admin Username field.
Google Sync Integration Guide
VMware, Inc. 12

Setting Description
Service Account Certificate
(*.p12)
Upload the Service account certificate. Enter the certificate password when
prompted. The certificate password is created while generating the Service
Account client ID on the Google console.
Directory service account email
address
Enter the Service Account email address that was generated while creating the
Service Account Certificate.
Application Name Enter the project name that you had created earlier.
4 Select Next.
5 In the Profiles wizard form, create a new profile or associate an existing profile. Select Next.
Result: The MEM Config Summary form provides a quick overview of the basic configuration
you have just created for the Gmail deployment.
6 Save the settings.
What to do next
After configuring your Gmail deployment, configure the advanced settings for the deployment.
Configure Gmail Deployment With Password Retention
If you have chosen to retain the password, then you can configure the settings to set up the
preferred password length.
Prerequisites
You must have configured the initial Gmail deployment settings.
Procedure
Google Sync Integration Guide
VMware, Inc. 13

Workspace ONE UEM does not provision passwords for newly enrolled devices or modifies the
password for the devices that change status when the email compliance policies are deactivated.
1 Navigate to the Email > Email Settings.
2 Deactivate the Use Default Settings to enter the preferred length of the password in the
Google Random Password Length field.
By default, the Use Default Settings check box is enabled. Minimum accepted character is 8
and maximum is 100.
3 Select the Rotate Profiles on Unenrollment check box to automatically rotate the password
and profiles of the existing devices whenever a device is unenrolled.
Also, if an administrator needs to manually rotate profiles and passwords outside of
enrollment or compliance, then navigate to the Accounts > Users, select a user, click MORE
ACTIONS, and select the Rotate G Suite password option.
4 Click Save.
Configure Gmail Deployment Without Password Retention
If you have chosen not to retain the password in the Workspace ONE UEM database, deactivate
the default settings which encrypts and stores the Google password in the Workspace ONE UEM
database.
The Email Compliance policies are not applicable for this type of integration. By default,
unmanaged devices are blocked.
Note Workspace ONE UEM provisions passwords to devices during enrollment regardless of the
MEM settings. The MDM compliance policies determines this approach.
Prerequisites
You must have configured the initial Gmail settings.
Google Sync Integration Guide
VMware, Inc. 14

Procedure
1 Navigate to Email > Email Settings.
2 Deactivate the Use Recommended Settings check box to configure the Google Apps
Settings options. By default, this option is enabled to encrypt and to store the Google
password in the Workspace ONE UEM database.
If a user has two devices enrolled and one of the devices unenrolls, the Google password
resets and a new generated password is pushed to the device that is enrolled.
3 Once you deactivate the Use Default Settings check box, configure the options.
Setting
Description
Google Random
Password Length
Enter the preferred random password length. Minimum accepted character is 8 and
maximum is 100.
Password Retention
Period
Enter the number of hours the password should be retained temporarily for management
purposes. The retention ensures that all the enrolled devices belonging to a user
receives the password. The default value is 48. The minimum accepted character is 1
and maximum is 100.
Auto-rotate Google
Password
Select this check box to reset the password once within the specific period. The
Scheduler runs to check if any user's password need to be reset within the specified
period. The minimum accepted character is 1 and maximum is 90.
Auto-rotate Google
Password Period
Enter the specific period to reset the Google password. The default period is 30 days.
4 Click Save.
Integrate Direct Model Using Directory APIs
Workspace ONE UEM manages email access on mobile devices without any password
management by using Google's Directory APIs.
Google Sync Integration Guide
VMware, Inc. 15

Enabling device activation blocks any unmanaged devices from accessing email. Workspace ONE
UEM checks with Google for a device account during enrollment when the profile is pushed onto
the device:
n If the enrolled device has an account, Google sends a positive response to Workspace ONE
UEM. Workspace ONE UEM then sends an approve command to Google to allow email
access.
n After the device enrolls, the profile is already installed on the device, and any attempt to
connect, creates a device record in Google. When the Google scheduler runs at a default
interval of five minutes, the device is identified and allowed for email access. The Email
Dashboard is then updated with the 'Scheduled Sync Update'.
n If the device fails to be identified by the scheduler after two days, then the end user must
login to SSP and select Sync Email for the device to receive email access.
Note You can also revoke access for Google accounts if an account violates compliance using
the Token Revocation option on the Email Settings page.
Prerequisites
Your device must have a Google account. If your device does not have a Google account setup
before enrolling in Workspace ONE UEM, then updates cannot be completed successfully and
the Email Dashboard on Workspace ONE UEM is updated with a "Failed" message.
Google Sync Integration Guide
VMware, Inc. 16

Procedure
1 Enable Device Activation on the Google Admin console:
a On the Google Admin console, navigate to Device Management > Mobile > Setup.
b On the Setup page, select Device Activation.
c Select an organization from the left panel and then select Require admin approval for
device activation.
d (Optional): Enter an email address to receive notifications when users enroll their devices.
You can also enter a group email address that includes all the administrators who can
activate the devices.
2 Configure Direct APIs Deployment Type on the UEM console:
a Navigate to Email > Email Settings and select Configure.The Email configuration wizard
displays.
Google Sync Integration Guide
VMware, Inc. 17

b Select Direct for the Deployment Model.
c Select Google Apps with Direct API as the Email Type.
d Click Next.
e In the Deployment Wizard form, enter the following settings:
Setting Description
Friendly Name Friendly name for the Gmail deployment.
Google Apps Domain Domain address
Google Apps Sub-Domain Sub-domain address
Google Apps Admin Username Complete email address
Service account certificate
(*.p12)
Upload the Service account certificate. Enter the certificate password
when prompted. The certificate password is created while generating the
Service Account client ID on the Google console.The type, validity, and
thumbprint of the certificate is displayed.
Directory service account email
address
Service Account email address.
Application Name Project name created earlier.
Enable Token Revocation Toggle Enable to make available the Revoke Google Token action within
MDM compliance policies.
The Revoke Google Token message is displayed on the MDM
compliance policy page.
Note: This option can only be enabled for one MEM configuration at a
time.
Automatically revoke when
wiping devices
Check this box to revoke G Suite token for the user upon unenrollment.
What to do next
If you have enabled token revocation, and the MDM policy is also set to revoke G Suite tokens
under Edit Device Policy, the token will be revoked for a non-compliant user. If you have also
enabled the Automatically revoke when wiping devices option, the G Suite token will be revoked
for the device when the device is unenrolled. See the
Mobile Email Management
guide.
Google Sync Integration Guide
VMware, Inc. 18

Create an Admin Role for Gmail
Integration
3
To manage Google users, Workspace ONE requires a Gmail administrator account with specific
privileges. Either a super user account or an administrator account with specific privileges can be
used.
Note If you choose to use a super admin account, skip to step 5. 2. Use a service account if you
do not want Workspace ONE to change or revoke the admin password from the Google console.
1 Log into your Google dashboard and navigate to Admin Roles.
2 Select Create A NEW ROLE.
VMware, Inc.
19

Result: Create New Role form displays.
3 Enter the Name and Description for the role, and then select Create.
4 On the Privileges tab, select the privileges for the new role.
The required privileges include:
n Admin console Privileges
n Organization Units - Read
n Users - Read
n Update - Rename users, Move users, Reset Password, Force Password, Add or
Remove Aliases, Suspend Users
n Security - To allow an admin with a custom role to revoke G tokens, enable the User
Security Management on both Admin console privileges and Admin API privileges.
Google Sync Integration Guide
VMware, Inc. 20

n Admin API Privileges
n Organization Units - Read
n Users - Read
n Update - Rename users, Move users, Reset Password, Force Password, Add/Remove
Aliases, Suspend Users
n Groups - To allow an admin with a custom role to revoke G tokens, enable the User
Security Management on both Admin console privileges and Admin API privileges.
5 Select Save.
6 Select the Admins tab and then Assign admins to assign the created role to an administrator
and then select Confirm Assignment.
Google Sync Integration Guide
VMware, Inc. 21

7
Enable the Google API
Use the Google control panel to enable the Google API.
For Workspace ONE UEM to provision the users' passcodes, enable the Google API using
the Google control panel. This is optional for Direct Integration with Directory API type of
configuration.
Procedure
1 Sign in to the Google Admin console.
2 Once logged in, navigate to Security > API Reference.
3 Check Enable API access.
4 Click Save.
Create a Service Account Certificate
The Service Account Certificate is required to use the Google APIs. You can create the certificate
from the Google Admin console and then upload it on the UEM console while configuring the
email integration.
Google Sync Integration Guide
VMware, Inc. 22
Procedure
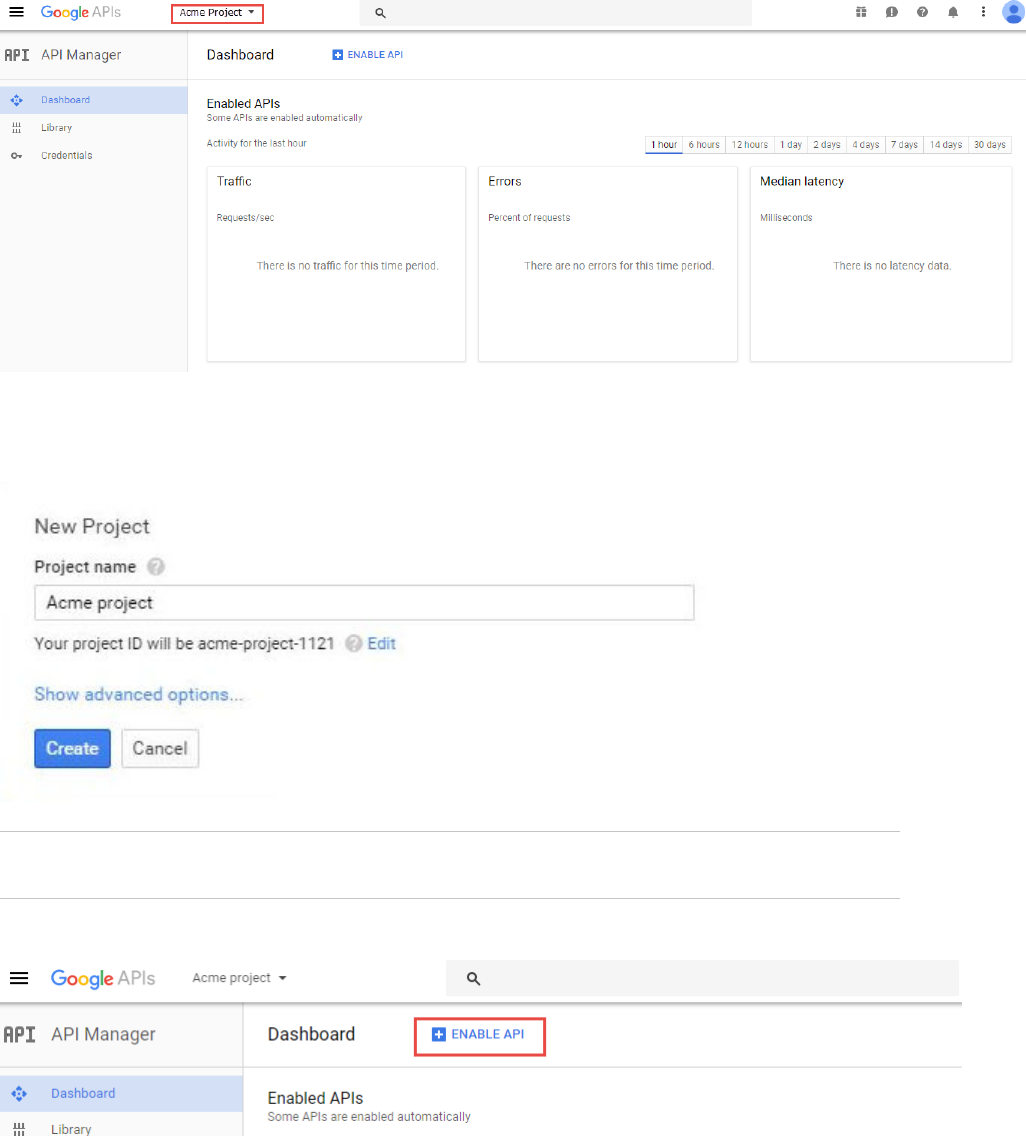
1 Navigate to https://console.developers.google.com and log in using your super admin
credentials. The API Dashboard page is displayed.
2 Select the projects list drop-down menu and then select + to create a project.
3 Enter the Project name and select Create. The project ID is generated.
Note The project ID cannot be changed once the project is created. In case you wish to
change the project ID, select Edit before you create the project.
4 Select Enable API.
5 Select Library from the API Manager sidebar.The list of Google APIs is displayed.
Google Sync Integration Guide
VMware, Inc. 23

6 Select Admin SDK available under G Suite APIs and then select Enable.
7 Select Credentials from the API Manager sidebar.
a On the Credentials page, elect Create credentials and then select Service account key.
b Select New service account from the Service account drop-down menu and provide the
Service account name, Service account ID, and the Role for the service account email
address.
c Select P12 as the Key type.
d Select Create. The new service account has been created. Save the .p12 certificate with
private key to your machine. Please make a note of the generated password for the
private key.
8 Select Manage service accounts on the credentials page.
9 Select the service account you created and then select Edit from the corresponding menu.
10 Check Enable G Suite Domain-wide Delegation check box. Click Save.
Google Sync Integration Guide
VMware, Inc. 24

Now, the Client ID is generated and the View Client ID appears under the Options for your
service account in the Service accounts page. Currently, there is no way to delete a Client ID
once the ID is generated. The only alternative is to delete and re-create the whole project.
Select View Client ID to view the generated Client ID and the service account email address.
11 Navigate to the Google Admin Console https://admin.google.com and login with your super
admin credentials.
12 Select Security > Advanced Settings.
13 Select Manage API client Access hyperlink from the Advanced settings pop-up menu.
14 Enter the previously generated Client ID (as mentioned in step 8 of On the Google Developer
console section) in the Client Name field.
15 Authorize your client ID for the required API scopes. Enter the API scopes for the applications
as listed in the One or More API Scopes field and then select Authorize
https://www.googleapis.com/auth/admin.directory.user,
https://www.googleapis.com/auth/admin.directory.user.readonly,
https://www.googleapis.com/auth/admin.directory.device.mobile.readonly,
https://www.googleapis.com/auth/admin.directory.device.mobile.action,
https://www.googleapis.com/auth/admin.directory.user.security
.
Note The API Scopes must be added as a comma-delimited string containing no spaces.
Google Sync Integration Guide
VMware, Inc. 25

Email Management through
Google Sync Integration
4
After the Gmail integration setup is complete, you can manage the connected device email
traffic, set email policies, and take appropriate actions on the devices from the UEM console.
Device Discovery
Before you can begin managing the device from the Email Dashboard, the configured
MEM should discover the devices enrolled to the organization group. On getting integrated with a
MEM deployment, devices are discovered either through one of the following:
n With EAS profile - Ensure all the managed devices receive the EAS profile.
n Without EAS profile - Profiles are a must for this type of deployment except while integrating
with Directory APIs. Unless the devices are provisioned with the profiles, the configured Gmail
deployment cannot identify and subsequently manage the device.
Note The features available here depends on the type of deployment that you choose.
Device Management with Direct Password Management
Integration
The Direct Integration using Password Management deployment does not involve
SEG integration, thus, the Email and Attachment Policies are not applicable.
If using the password retention approach, you can use the compliance policies and the Email
Dashboard to manage the devices and view the device status. If you choose not to retain the
password, then the email policies are not applicable and the device status is not displayed on the
Email Dashboard.
With Password Retention
n Managed Device Polices
Activate the following policies from Email > Compliance Policies page. .
n Inactivity – Allows you to prevent inactive, managed devices from accessing email. You
can specify the number of days a device shows up as inactive (that is, does not check in
to Workspace ONE), before email access is cut off.
VMware, Inc.
26
n Device Compromised – Allows you to prevent compromised devices from accessing
email. Note that this policy does not block email access for devices that have not
reported compromised status to Workspace ONE.
n Encryption – Allows you to prevent email access for unencrypted devices. Note that
this policy is applicable only to devices that have reported data protection status to
Workspace ONE.
n Model – Allows you to restrict email access based on the Platform and Model of the
device.
n Operating System – Allows you to restrict email access to a set of operating systems for
specific platforms.
n Require ActiveSync Profile - Allows you to restrict email access to devices whose email is
managed through an Exchange ActiveSync profile.
n Email Dashboard
Access the Email Dashboard page from Email > Dashboard. The Actions drop-down menu
provides a single location to perform multiple actions on the device. Select the check box
corresponding to a device to perform actions on it.
n Allowed - Allows a device to receive emails
n Blocked - Blocks a device from receiving emails
n Default - Allows or blocks a device based on whether the device is compliant or non-
compliant
Without Password Retention
n Device Compliance Policies
In this type of deployment, email compliance policies are not applicable. You can only
assign the device compliance policies that are available at Devices > Compliance Policies
> List View. You can set these policies as 'Remove EAS Profile' to ensure removal of email
connectivity once the device is found to be non compliant.
n Device Dashboard
In this type of deployment, Email Dashboard does not display the devices. You can view and
manage devices of this deployment through the Device Dashboard available at Devices >
Dashboard.
Device Management with Directory APIs Integration
Manage your devices using the email compliance policies that are applicable for Directory APIs
configuration. Along with the compliance policies, the Email Dashboard and the List View page
also lets you effectively manage your corporate devices.
While the Email Dashboard displays the device status, the List View page displays user and
device-specific information either in a summarized or detailed manner.
Google Sync Integration Guide
VMware, Inc. 27

General Policies
n Managed device – Allow/block unenrolled devices from accessing email.
Managed Device Polices
Note Workspace ONE does not set access against Google for any devices that enroll while
compliance is deactivated, nor change the access state for any previously enrolled devices that
change compliance status.
The policies mentioned here can be activated from Email > Compliance Policies page.
n Inactivity – Allows you to prevent inactive, managed devices from accessing email. You can
specify the number of days a device shows up as inactive (that is, does not check-in to
Workspace ONE), before email access is cut off.
n Device Compromised – Allows you to prevent compromised devices from accessing email.
Note that this policy does not block email access for devices that have not reported
compromised status to Workspace ONE.
Note Unenrolled devices are blocked by default.
n Encryption – Allows you to prevent email access for unencrypted devices. Note that this
policy is applicable only to devices that have reported data protection status to Workspace
ONE.
n Model – Allows you to restrict email access based on the Platform and Model of the device.
n Operating System – Allows you to restrict email access to a set of operating systems for
specific platforms.
n Require ActiveSync Profile – Allows you to restrict email access to devices whose email is
managed through an Exchange ActiveSync profile.
Email Dashboard
Gain visibility into the email traffic and monitor the devices through the Workspace ONE
Email Dashboard. This dashboard gives you a real-time summary of the status of the devices
connected to the email traffic. You can access the Dashboard from Email > Dashboard. The email
dashboard enables you to perform the following actions:
n Allowlist or denylist a device to allow or deny access of email
n View the devices which are managed, unmanaged, compliant, non- compliant, blocked, or
allowed
n View the device details such as OS, Model, Platform, Phone Number, IMEI, IP address
Google Sync Integration Guide
VMware, Inc. 28

From the Dashboard, you can also use the available Graphs to filter your search. For example,
if you want to view all the managed devices of that organization group, select the Managed
Devices graph. This displays the results in the List View screen.
List View
View all the real-time updates of your end user devices that you are managing with Workspace
ONE MEM. You can access the List View from Email > List View. You can view the device or
user-specific information by switching between the two tabs: Device and User. You can change
the Layout to either view the summary or the detailed list of the information based on your
requirement.
The List View screen provides detailed information that includes:
n Last Request – The last state change of the device. In SEG integration, this column shows the
last time a device synced mail.
n User – The user account name.
n Friendly Name – The friendly name of the device.
n MEM Config – The configured MEM deployment that is managing the device.
n Email Address – The email address of the user account.
n Identifier – The unique alpha-numeric identification code associated with the device.
n Mail Client – The email client syncing the emails on the device.
n Last Command – The command triggers the last state change of the device and populates
the Last Request column.
Google Sync Integration Guide
VMware, Inc. 29

n Last Gateway Server – The gateway server to which the device connected.
n Status – The real time status of the device and whether email is blocked or allowed on it as
per the defined policy.
n Reason – The reason code for allowing or blocking email on a device.
Note The reason code displays 'Global' when access state is defined by the default organization
allow/block/quarantine policy. The reason code is 'Individual' when device ID is explicitly set for a
given mailbox by Exchange admin or Workspace ONE. The reason code is 'Policy' when device is
blocked by any EAS policy.
n Platform, Model, OS, IMEI, EAS Device Type, IP Address – The device information displays
in these fields.
n Mailbox Identity – The location of the user mailbox in the Active Directory.
Filters for Quick Search
The Filter option is available on the List View page. Using this filter, you can narrow your device
search based on:
n Last Seen – All, less than 24 hours, 12 hours, 6 hours, 2 hours.
n Managed – All, Managed, Unmanaged.
n Allowed – All, Allowed, Blocked.
n Policy Override – All, blocked, allowed, Default.
n Policy Violation – Compromised, Device Inactive, Not data Protected/Enrolled/MDM
Compliant, Unapproved EAS Device Type/Email Account/Mail Client/Model/OS.
n MEM Config – Filter devices based on the configured MEM deployments.
Performing Actions
The Override, Actions, and Administration drop-down menu provides a single location to
perform multiple actions on the device.
Note Note that these actions once performed cannot be undone.
n Override
Select the check box corresponding to a device to perform actions on it.
n Allowed – Allows a device to receive emails.
n Blocked – Blocks a device from receiving emails.
n Default – Allows or blocks a device based on whether the device is compliant or non-
compliant.
Google Sync Integration Guide
VMware, Inc. 30

n Actions
n Run Compliance – Triggers the compliance engine to run for the selected MEM
configuration. For any device that has a state change (that is, compliant to non-compliant
or conversely), Workspace ONE sends out an Allow/Block command accordingly.
n Administration
n Remote Wipe – Resets the device to factory settings.
n Migrate Devices – Migrates selected device to other chosen MEM configurations by
deleting the installed EAS profile and pushing the EAS profile of the chosen configuration
on the device.
Testing the email policies before deploying on the devices is a good practice. Workspace ONE
recommends using the following method to test the capabilities of these policies before applying
them on the devices.
Deactivate the Compliance option available on the Email Policies page during the testing phase.
Use separate organization groups to test out policies against a subset of enrollment users who
also belong to the Gmail environment.
Device Management with SEG Proxy Integration
Manage your devices with the email compliance policies applicable for SEG Proxy configuration.
These compliance policies help you prevent non-compliant, unmanaged, or blocked devices from
accessing corporate emails.
Apart from compliance policies, you can also use the Email dashboard and the list view page
to effectively manage your corporate devices. You can view the status of the devices using the
Email Dashboard and the user-specific or device-specific information using the List View page.
Note Workspace ONE UEM will not provision passwords for new users, but SEG will continue to
proxy the requests for devices that were previously enrolled successfully to Google.
Compliance Policies
The compliance policies mentioned in this section can be activated from the Email > Compliance
Policies page.
n General Email Policies
n Sync Settings – Prevent the device from syncing with specific EAS folders. Note
that Workspace ONE UEM prevents devices from syncing with the selected folders
irrespective of other compliance policies. For the policy to take effect, you must republish
the EAS profile to the devices (this forces devices to resync with the email server).
n Managed Device – Restrict email access only to managed devices.
n Mail Client – Restrict email access to a set of mail clients.
n User – Restrict email access to a set of users.
Google Sync Integration Guide
VMware, Inc. 31
n EAS Device Type – Allow or block devices based on the EAS Device Type attribute
reported by the end-user device.
n Managed Device Policies
n Inactivity – Allows you to prevent inactive, managed devices from accessing email. You
can specify the number of days a device shows up as inactive (that is, does not check in
to Workspace ONE UEM), before email access is cut off.
n Device Compromised – Allows you to prevent compromised devices from accessing
email. Note that this policy does not block email access for devices that have not
reported compromised status to Workspace ONE UEM.
n Encryption – Allows you to prevent email access for unencrypted devices. Note that
this policy is applicable only to devices that have reported data protection status to
Workspace ONE UEM.
n Model – Allows you to restrict email access based on the Platform and Model of the
device.
n Operating System – Allows you to restrict email access to a set of operating systems for
specific platforms.
n Require ActiveSync Profile - Allows you to restrict email access to devices whose email is
managed through an Exchange ActiveSync profile.
n Email Security Policies
n Email Security Classification – You may either allow or block the emails on email clients.
n Attachments (managed devices) – Encrypt email attachments of the selected file types.
These attachments are secured on the device and are only available for viewing on
the VMware Content Locker. Currently, this feature is only available on managed iOS,
Android, and Windows Phone devices with the VMware Content Locker application. For
other managed devices, you can choose to either allow encrypted attachments, block
attachments, or allow unencrypted attachments.
n Attachments (unmanaged devices) – Allow encrypted attachments, block attachments,
or allow unencrypted attachments for unmanaged devices.
n Hyperlink – Allow device users to open hyperlinks contained within an email directly with
Workspace ONE Web present on the device. The Secure Email Gateway dynamically
modifies the hyperlink to open in Workspace ONE Web. You may choose one of the
following modification types:
n All - Choose to open all the hyperlinks with Workspace ONE Web.
n Include - Choose if you want the device users to open only the hyperlinks through the
Workspace ONE Web. Mention the included domains in the Only modify hyperlinks
for these domains field. You can bulk upload the domain names from a CSV file as
well.
Google Sync Integration Guide
VMware, Inc. 32

n Exclude - Choose if you do not want the device users to open the mentioned domains
through the Workspace ONE Web. Mention the excluded domains in the Modify all
hyperlinks except for these domains field. You can bulk upload the domain names
from a CSV file as well.
Email Dashboard
Gain visibility into the email traffic and monitor the devices through the Workspace ONE UEM
Email Dashboard. This dashboard gives you a real-time summary of the status of the devices
connected to the email traffic. You can access the dashboard from Email > Dashboard. The email
dashboard enables you to:
n Allowlist or denylist a device to allow or deny access of email
n View the devices which are managed, unmanaged, compliant, non- compliant, blocked, or
allowed
n View the device details such as OS, Model, Platform, Phone Number, IMEI, IP address
From the Dashboard, you can also use the available Graphs to filter your search. For example,
if you want to view all the managed devices of that organization group, select the Managed
Devices graph. This displays the results in the List View screen.
List View
Google Sync Integration Guide
VMware, Inc. 33

View all the real-time updates of your end user devices that you are managing with Workspace
ONE UEM. You can access the List View from Email > List View. You can view the device or
user-specific information by switching between the two tabs: Device and User. You can change
the Layout to either view the summary or the detailed list of the information based on your
requirement.
The List View screen provides detailed information that includes:
n Last Request - In PowerShell integration, this column displays the last state change of the
device either from Workspace ONE UEM or from Exchange. In SEG integration, this column
shows the last time a device synced mail.
n User - The user account name.
n Friendly Name - The friendly name of the device.
n MEM Config - The configured MEM deployment that is managing the device.
n Email Address - The email address of the user account.
n Identifier - The unique alpha-numeric identification code associated with the device.
n Mail Client - The email client syncing the emails on the device.
n Last Command - The command triggers the last state change of the device and populates
the Last Request column.
n Last Gateway Server -The server to which the device connected.
n Status - The real time status of the device and whether email is blocked or allowed on it as
per the defined policy.
n Reason - The reason code for allowing or blocking email on a device.
Note The reason code displays 'Global' when access state is defined by the default organization
allow/block/quarantine policy. The reason code is 'Individual' when device ID is explicitly set for
a given mailbox by Exchange admin or Workspace ONE UEM. The reason code is 'Policy' when
device is blocked by any EAS policy.
n Platform, Model, OS, IMEI, EAS Device Type, IP Address - The device information displays in
these fields.
n Mailbox Identity - The location of the user mailbox in the Active Directory.
Filters for Quick Search
The Filter option is available on the List View page. Using this filter, you can narrow your device
search based on:
n Last Seen - All, less than 24 hours, 12 hours, 6 hours, 2 hours.
n Managed - All, Managed, Unmanaged.
n Allowed - All, Allowed, Blocked.
n Policy Override: All, Blocked, Allowed, Default.
Google Sync Integration Guide
VMware, Inc. 34

n Policy Violation - Compromised, Device Inactive, Not data Protected/Enrolled/MDM
Compliant, Unapproved EAS Device Type/Email Account/Mail Client/Model/OS.
n MEM Config - Filter devices based on the configured MEM deployments.
Performing Actions
The Override, Actions and Administration drop-down menu provides a single location to
perform multiple actions on the device.
Note Please note that these actions once performed cannot be undone.
n Override
Select the check box corresponding to a device to perform actions on it.
n Allowed - Allows a device to receive emails.
n Blocked - Blocks a device from receiving emails.
n Default - Allows or blocks a device based on whether the device is compliant or non-
compliant.
n Actions
n Run Compliance - Triggers the compliance engine to run for the selected MEM
configuration. For any device that has a state change (that is, compliant to non-compliant
or conversely), Workspace ONE sends out an Allow/Block command accordingly.
n Test Mode - Tests email policies without applying them on devices.
n Administration
n Dx Mode On - Runs the diagnostic for the selected user mailbox providing you the history
of the device activity. After enabling this option, Workspace ONE starts recording the
activity of the device. This feature is available for SEG only.
n Dx Mode Off - Turns off the diagnostic for the selected user mailbox. This feature is
available for SEG only.
n Update Encryption Key - Resets the encryption and the resyncs the emails for the
selected devices. This feature is available for SEG only.
n Delete Unmanaged Devices - Deletes the selected unmanaged device record from the
dashboard. Please note that this record may reappear after the next sync.
n Migrate Devices - Migrates selected device to other chosen MEM configurations by
deleting the installed EAS profile and pushing the EAS profile of the chosen configuration
on the device.
Google Sync Integration Guide
VMware, Inc. 35
