
ArcGIS Online
Higher Education Information Security Council (HEISC) Higher Education Community Vendor Assessment Tool
(HECVAT Lite) 3.04 July 2023
Attached are Esri’s self-assessment answers to the Higher Education Information Security Council (HEISC) Higher Education Community Vendor Assessment Tool
(HECVAT Lite) for ArcGIS Online. The questionnaire published by the HEISC, provides a comprehensive understanding of the security measures implemented by
ArcGIS Online using the HECVAT Lite framework. Essential to higher education institutions, the HECVAT Lite helps to ensure strong information security and
security control practices, updated security programs, and effective incident response plans. This is designed for IT professionals and administrators in higher
education to assist institutions in making informed decisions in the use of ArcGIS Online securely and in compliance with their institution's policies.
The Higher Education Information Security Council (HEISC) is a collaborative body that supports higher education institutions as they improve information security
governance, compliance, data protection, and privacy programs. The council, formed under EDUCAUSE, a nonprofit association that advances higher education
using information technology, is dedicated to enhancing the state of information security and privacy across the higher education sector.
ArcGIS Online is audited annually by a 3rd party assessor to ensure alignment with its Federal Risk and Authorization Management Program (FedRAMP) Authority
to Operate (ATO) by the United States Department of Interior. For more information concerning the security, privacy, and compliance of ArcGIS Online please see
the ArcGIS Trust Center at: https://Trust.ArcGIS.com
ArcGIS Online utilizes the World-Class Cloud Infrastructure of Microsoft Azure and Amazon Web Services, both of which have completed HECVAT questionnaires
for their capabilities and may be viewed at the Amazon Web Services and Microsoft Azure websites.
The latest version of the ArcGIS Online HECVAT Lite answers will be available at the following location until further notice:
https://downloads.esri.com/resources/enterprisegis/AGOL_HECVAT.pdf
For a more lightweight set of answers, a basic overview of ArcGIS Online security (2-page flyer) is available within the Trust Center documents. Some basic,
recurring customer questions include:
• Where is my data hosted? Within AWS and MS Azure datacenters on US Soil by default, new organizations can choose to have their data stored in regions
outside the US, such as the EU or AP Regions.
• Is my data encrypted at rest and in transit? Yes, organizations use HTTPS w/TLS 1.2 for in-transit and AES-256 at rest.
• Is my data backed up? Customers are responsible for backing up their datasets.
• Can I do security tests against ArcGIS Online? Yes, however a Security Assessment Agreement (SAA) must be completed first.
• Are my files scanned with Anti-virus? Yes – Files containing malicious code are rejected from upload.
• What privacy assurance is in place? ArcGIS Online is both GDPR and CCPA aligned.
For any questions/concerns/feedback please contact Esri’s Software Security & Privacy Team at:

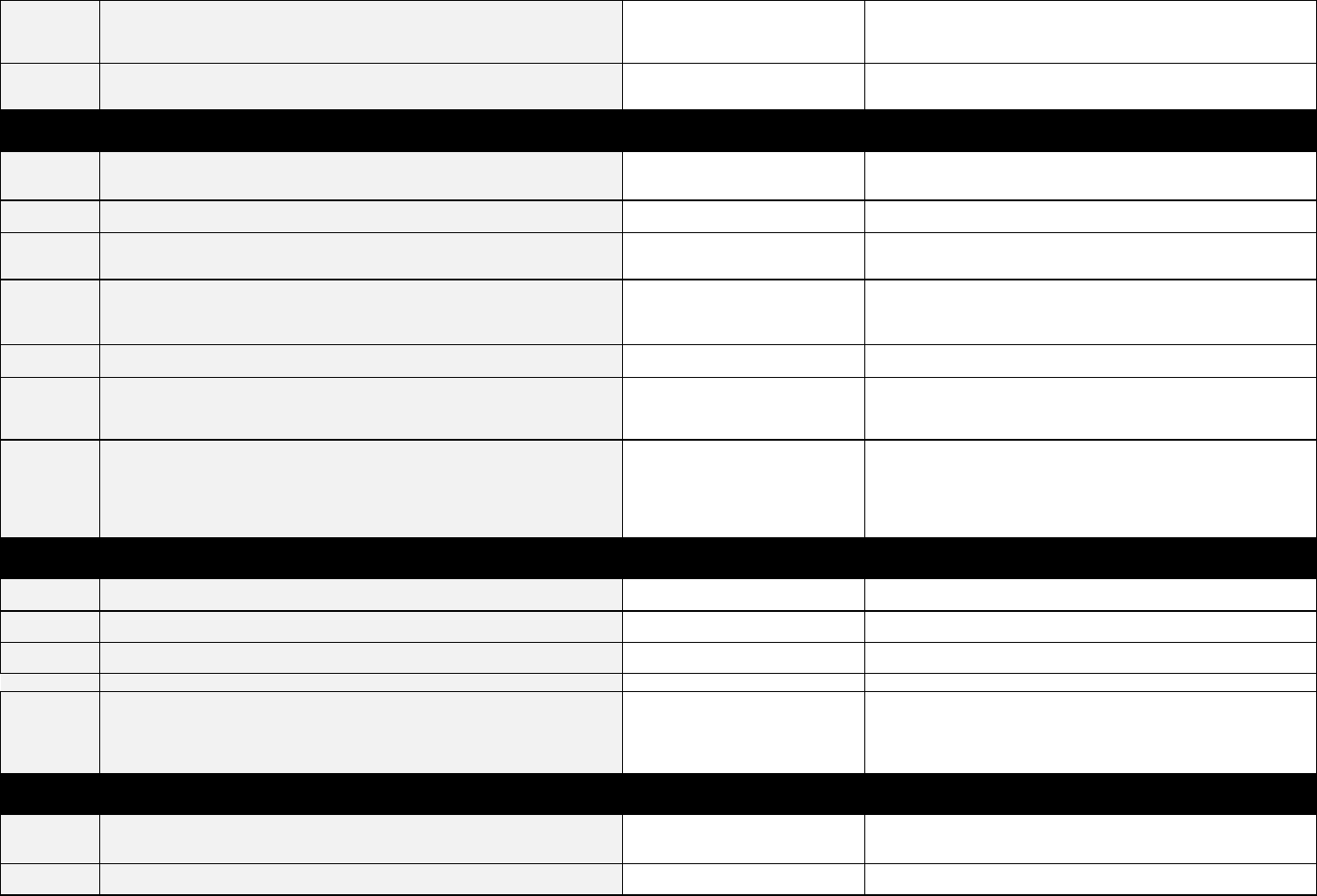
ARCGIS ONLINE HECVAT LITE V 3.04
DATE-01
Date
GNRL-01 Vendor Name
GNRL-02 Product Name
GNRL-03 Product Description
GNRL-04 Web Link to Product Privacy Notice
GNRL-05 Web Link to Accessibility Statement or VPAT
GNRL-06 Vendor Contact Name
GNRL-07 Vendor Contact Title
GNRL-08 Vendor Contact Email
GNRL-09 Vendor Contact Phone Number
GNRL-10 Vendor Accessibility Contact Name
GNRL-11 Vendor Accessibility Contact Title
GNRL-12 Vendor Accessibility Contact Email
GNRL-13 Vendor Accessibility Contact Phone Number
GNRL-14 Vendor Hosting Regions
GNRL-15 Vendor Work Locations
Vendor Answers Additional Information
COMP-01
Describe your or
g
anization’s business back
g
round and ownership structure,
includin
g
all
p
arent and subsidiar
y
relationshi
p
s
.
COMP-02
Have you had an unplanned disruption to this product/service in the last 12
months?
No
Seestatus.arcgis.com
COMP-03 Do you have a dedicated Information Security staff or office? Yes
Esri'sSoftwareSecurity&Privacyteamisdedicatedtothesecurityandprivacy
assuranceofourproducts.
COMP-04
Do you have a dedicated Software and System Development team(s)? (e.g.
Customer Support, Implementation, Product Management, etc.)
Yes
SeeEsri.comforcompanystructuredetails.
COMP-05
Does your product process protected health information (PHI) or any data
covered by the Health Insurance Portability and Accountability Act?
No
DatasetsuploadedtoArcGISOnlineareownedbythecustomerandtheyare
responsibleforclassifyingtheirdatasetandhandlingaccordingly.
ItistheCustomer's
soleresponsibilitytoensurethatCustomerContentissuitableforusewithOnline
Services.ArcGISOnlinehasselectHIPAAeligableservicesavailableasdescribed
withintheArcGISTrustCenter
HECVAT - Lite | Vendor Response
Vendor Response
4/22/2023
General Information
In order to protect the institution and its systems, vendors whose products and/or services will access and/or host institutional data must complete the Higher Education Community
Vendor Assessment Toolkit. Throughout this tool, anywhere where the term data is used, this is an all-encompassing term including at least data and metadata. Answers will be
reviewed by institution security analysts upon submittal. This process will assist the institution in preventing breaches of protected information and comply with institution policy, state,
and federal law. This is intended for use by vendors participating in a Third Party Security Assessment and should be completed by a vendor.
Esri
ArcGISOnline
ArcGISOnlineisasecured,reliablegeographicinformationsystem(GIS)deliveredusingthesoftware‐as‐a‐service(SaaS)model.
https://www.vendor.domain/privacynotice
https://www.esri.com/content/dam/esrisites/en‐us/media/legal/vpats/arcgis‐online‐march‐2022‐vpat.pdf
Esri
SoftwareSecurityandPrivacyTeam
909‐793‐2853
EsriAccessibilityTeam
Vendor Instructions
Step 1: Complete each section answering each set of questions in order from top to bottom; the built-in formatting logic relies on this order. Step 2: Submit the completed Higher
Education Community Vendor Assessment Toolkit - Lite to the requesting institution.
Company Overview
Private Geo
g
raphic Information System (GIS) software vendor with
g
lobal distributor
s
EsriAccessibilityTeam
909‐793‐2853
BydefaultallArcGISOnlinecustomerdataresidesonUnitedStatessoilwithintheconfinesoftheAmazonWebServiceUSRegions
Redlands,CA
July 2023 Page 1

ARCGIS ONLINE HECVAT LITE V 3.04
COMP-06 Will data regulated by PCI DSS reside in the vended product? No
Esristoresnopaymentinstrumentnumberinformation(e.g.creditcard)withintheir
systemsforProducts&Services.Esriutilizesathirdpartyproviderwhichhasbeen
auditedbyaPaymentCardIndustryStandardcertifiedauditortoensureyour
informationremainssecure.Paymentinformationistransmitteddirectlytothe
providervia
HTTPSforsecuretransmissionsothatpaymentdataisnever
transmittedorstoredb
y
EsriProducts&Services.
COMP-07
Use this area to share information about your environment that will assist thos
e
who are assessin
g
y
our com
p
an
y
data securit
y
p
ro
g
ram.
Vendor Answers Additional Information
DOCU-01 Have you undergone a SSAE 18 / SOC 2 audit? No
NoplanforSSAE16asFedRAMPTailoredLowauthorizationinplaceismore
comprehensive
DOCU-02 Have you completed the Cloud Security Alliance (CSA) CAIQ? Yes
ArcGISOnlinestandardsarebasedonFedRAMPTailoredLowrequirements.Also,
thisCloudSecurityAlliance(CSA)CAIQforArcGISOnlineisavailabletocustomers
andcanbeviewedhere:
https://downloads.esri.com/RESOURCES/ENTERPRISEGIS/AGOL_CSA_CAIQ.PDF
DOCU-03 Have you received the Cloud Security Alliance STAR certification? No
EsriArcGISOnlineisSTAR
LevelOnesince8/19/2015.CurrentCAIQcanbeviewedon
ourArcGISTrustCenter:
https://downloads.esri.com/RESOURCES/ENTERPRISEGIS/AGOL_CSA_CAIQ.PDF
DOCU-04
Do you conform with a specific industry standard security framework? (e.g.
NIST Cybersecurity Framework, CIS Controls, ISO 27001, etc.)
Yes
ArcGISOnlineisFedRAMPauthorizedwhichisbasedonNISTsecuritycontrols.
DOCU-05
Can the systems that hold the institution's data be compliant with NIST SP 800-
171 and/or CMMC Level 3 standards?
Yes
ArcGISOnlineisFedRAMPauthorizedwhichisbasedonNISTsecuritycontrols.The
offeringisshiftingfromTailoredLowtoModerate
in2023.NIST800‐171isasubset
ofFedRAMPModeratesecuritycontrols.
DOCU-06
Can you provide overall system and/or application architecture diagrams
including a full description of the data flow for all components of the system?
Yes
Pleasereviewthisonlineresourceformoreinformation:
https://downloads.esri.com/resources/enterprisegis/ArcGIS_Online_Security.pdf
DOCU-07 Does your organization have a data privacy policy? Yes
Esri'sPrivacyStatementandProducts&ServicesPrivacyStatementSupplementare
availableonourTrustCenter:https://trust.arcgis.com/en/privacy/privacy‐tab‐
intro.htm
DOCU-08
Do you have a documented, and currently implemented, employee onboarding
and offboarding policy?
Yes
Allemployeesmusthaveabackground
checkbeforebeingonboardedintoArcGIS
Online‐Employeesaccessisremovedsamedayasoffboarding.
DOCU-09
Do you have a well documented Business Continuity Plan (BCP) that is tested
annually?
Yes
ArcGISOnlinehasafullContinuityPlandesignedinalignmentwithFedRAMP
TailoredLowsecuritycontrolrequirements.ArcGISOnlinecloudInfrastructure
p
rovidersensuretheirbusinesscontinuit
y
p
lansali
g
nwithISO27001standards.
DOCU-10
Do you have a well documented Disaster Recovery Plan (DRP) that is tested
annually?
Yes
TheDRPisrequiredforFedRAMPandassessedannuallybya3rdparty.
DOCU-11 Do you have a documented change management process? Yes
AllchangestotheArcGISOnlineinfrastructurearetrackedandrecordedthroughthe
ChangeManagementdocumentedprocessesandProcedures,scheduled
maintenancewindowsarepublishedtotheArcGISOnlineStatusdashboardwhere
an
y
customercansubscribetoforu
p
datesathtt
p
s:
//
status.arc
g
is.com.
DOCU-12
Has a VPAT or ACR been created or updated for the product and version under
consideration within the
p
ast
y
ear
?
Yes
https://www.esri.com/en-us/legal/accessibility/conformance-
reports
DOCU-13
Do you have documentation to support the accessibility features of your
product?
Yes
Pleasereviewthefollowinghttps://www.esri.com/en‐us/accessibility/overview.This
includesresourcesandconformancereportsforourcoreproductsincludingArcGIS
Online.
See the ArcGIS Trust Center for details about ArcGIS Online Security & Privacy
Documentation
July 2023 Page 2

ARCGIS ONLINE HECVAT LITE V 3.04
Vendor Answers Additional Information
ITAC-01
Has a third party expert conducted an accessibility audit of the most recent
version of your product?
Yes
April15,2022theproductwastestedbycertifiedaccessbilityprofessionalsandthe
EsriAccessbilityConformanceReportcanbeviewedhere:
https://www.esri.com/content/dam/esrisites/en‐us/media/legal/vpats/arcgis‐online‐
march‐2022‐v
p
at.
p
df
ITAC-02
Do you have a documented and implemented process for verifying accessibility
conformance?
Yes
Pleasereviewthefollowinghttps://www.esri.com/en‐us/accessibility/overview.This
includesresourcesandconformancereportsforourcoreproductsincludingArcGIS
Online.
ITAC-03
Have you adopted a technical or legal accessibility standard of conformance for
the product in question?
Yes
Pleaseseethefollowinglinkfordetails:https://www.esri.com/en‐
us/legal/accessibility/accessibility‐overview
ITAC-04
Can you provide a current, detailed accessibility roadmap with delivery
timelines?
Yes
FordetailstothelatestapproachtoaccessibilityatEsri,pleaseseethefollowing
page:https://www.esri.com/en‐
us/accessibility/overview
ITAC-05 Do you expect your staff to maintain a current skill set in IT accessibility? Yes
Yes,Esrihasadedicatedaccessibilityteamwho'seffortistoachieveproduct
accessibilityforallbeginswithdiligentresearchofevolvingaccessibilitycapabilities
andcontinueswiththedevelopmentandincorporationofthesecapabilitiesintoGIS
functionsacrossourproductline.
ITAC-06
Do you have a documented and implemented process for reporting and
tracking accessibility issues?
Yes
Ourcoreproductdevelopmentteamsconductaccessibility
testingeventsandare
providedwithtestingtools,resourcesandmaterials,andinternalsupportfrom
accessibilit
y
sub
j
ectmatterex
p
erts
(
SMEs
)
throu
g
houtthecom
p
an
y
.
ITAC-07
Do you have documented processes and procedures for implementing
accessibility into your development lifecycle?
Yes
Esrirecognizestheimportanceofadheringtoaccessibilityguidelinesandstandards
forallusersofourproducts,includinguserswithdisabilities.Weconduct
AccessibilityConformanceReports(ACR®)forEsriproducts,solutions,andservices.
Eachreportdescribestheconformancelevelforaccessibilityfeatures,assistive
technologies,andevaluationmethodsused,
withadditionalinformationabout
generalproductaccessibility.Weincorporateinclusivedesignprinciplesthroughout
thecreationofEsricoresoftware,website,anddesignsystems.Ourongoingmission
isreflectedintheusabilityofourproductsandsolutions.
EsriutilizestheBuildingSecurityInMaturityModel(BSIMM)asthebackboneto
measureits
effortstoimmersesecuritythroughoutthedevelopmentlifecycleinthe
mosteffectivemannerforitsproducts.ArcGISOnlineisFedRAMPTailoredLow
authorizedandthereforealsoalignswithNISTstandards.
PleaseseeourSecureDevelopmentLifecycleOverviewonwithintheArcGISTrust
Center documents https://trust arcgis com for more information
ITAC-08
Can all functions of the application or service be performed using only the
keyboard?
Yes
Pleaseseethefollowingdocumentationfordetails:
https://www.esri.com/content/dam/esrisites/en‐us/media/legal/vpats/arcgis‐online‐
march‐2022‐vpat.pdf
ITAC-09
Does your product rely on activatin
g
a special ‘accessibility mode,’ a ‘lite
version’ or accessin
g
an alternate interface for accessibilit
y
p
ur
p
oses
?
No
Vendor Answers Additional Information
HLAP-01
Are access controls for institutional accounts based on structured rules, such as
role-based access control (RBAC), attribute-based access control (ABAC) or
p
olic
y
-based access control
(
PBAC
)
?
Yes
ArcGISOnlinereliesontheRoleBasedAccessControl(RBAC)model.Allusersin
solutionneedtohavearoleforwhichtheyaregrantedaccessto.
IT Accessibility
Application/Service Security
July 2023 Page 3

ARCGIS ONLINE HECVAT LITE V 3.04
HLAP-02
Are access controls for staff within your organization based on structured rules,
such as RBAC, ABAC, or PBAC?
Yes
ArcGISOnlinereliesontheRoleBasedAccessControl(RBAC)model.Allusersin
solutionneedtohavearoleforwhichtheyaregranted
accessto.
HLAP-03
Do you have a documented and currently implemented strate
g
y for securin
g
employee workstations when they work remotely? (i.e. not in a trusted
com
p
utin
g
environment
)
Yes
Yes,thereisanemployeeworkfromhomeguide.
HLAP-04 Does the system provide data input validation and error messages? Yes
Seeonlinehelphere:https://developers.arcgis.com/net/reference/platform‐error‐
codes/
HLAP-05 Are you using a web application firewall (WAF)? Yes
HLAP-06
Do you have a process and implemented procedures for mana
g
in
g
your
software su
pp
l
y
chain
(
e.
g
. libraries
,
re
p
ositories
,
frameworks
,
etc
)
Yes
SeeEsriSoftwareSecurityOverviewdocumentwithintheArcGISTrustCenter.
Vendor Answers Additional Information
HLAA-01
Does your solution support single sign-on (SSO) protocols for user and
administrator authentication?
Yes
OrganizationscanchoosetoutilizeArcGISOnlineOrganizationSpecificLogins(Esri's
versionofSSO‐usingtheSAMLstandard)tomeetalloftheirorganization’s
usernameandpasswordmanagementrequirementsandforadherencetoFedRAMP
andISO27001securityrequirements.
HLAA-02
Does your organization participate in InCommon or another eduGAIN affiliated
trust federation?
Yes
ArcGISOnlinesupportsfederationofidentityproviders
asdocumentedhere:
https://doc.arcgis.com/en/arcgis‐online/administer/saml‐logins.htm
HLAA-03
Does your application support integration with other authentication and
authorization systems?
Yes
Customersareresponsibleformanagingauthentication&accesstotheirtheArcGIS
OnlineapplicationusingaSAML2.0compliantIdentityProvider(IdP).
HLAA-04
Does your solution support any of the following Web SSO standards? [e.g.,
SAML2 (with redirect flow), OIDC, CAS, or other]
Yes
SAML2.0,Oauth
HLAA-05 Do you support differentiation between email address and user identifier? Yes Oneemailcanbeassociatedwithmultipleaccounts.
HLAA-06
Do you allow the customer to specify attribute mappin
g
s for any needed
information beyond a user identifier? [e.g., Reference eduPerson,
ePPA
/
ePPN
/
ePE
]
Yes
Groupinformation
HLAA-07
Are audit lo
g
s available to the institution that include AT LEAST all of the
followin
g;
lo
g
in
,
lo
g
out
,
actions
p
erformed
,
timestam
p,
and source IP address
?
Yes
SeetheArcGISOnlineHistoryAPI
HLAA-08
If you don't support SSO, does your application and/or user-frontend/portal
support multi-factor authentication? (e.g. Duo, Google Authenticator, OTP, etc.)
Yes
SSOissupported,butMFAcanbeusedwithArcGISOnlinebuilt‐inaccounts
HLAA-09
Does your application automatically lock the session or lo
g
-out an account after
a
p
eriod of inactivit
y?
No
ArcGISOnlineissessionless
Vendor Answers Additional Information
HLSY-01
Do you have a systems mana
g
ement and confi
g
uration strate
g
y that
encompasses servers, appliances, cloud services, applications, and mobile
devices
(
com
p
an
y
and em
p
lo
y
ee owned
)
?
Yes
SystemsintheArcGISOnlinesolutionaremanagedinalignmentwithFedRAMP
TailoredLowrequirements,whichincluderegularoperatingsystemupdatesandhot
fixes.AnyhardwareupdatesareperformedbytheCSP.
HLSY-02
Will the institution be notified of major changes to your environment that could
impact the institution's security posture?
Yes
Seestatuspageoftrust.arcgis.com
HLSY-03
Are your systems and applications scanned for vulnerabilities [that are then
remediated] prior to new releases?
Yes
VulnerabilityassessmentsagainstArcGISOnlineareconductedatleastmonthly
as
partoftheContinuousMonitoringPlan‐includingsystem,webapplicationand
databasescans.
Authentication, Authorization, and Accounting
Systems Management
July 2023 Page 4
ARCGIS ONLINE HECVAT LITE V 3.04
HLSY-04
Have your systems and applications had a third party security assessment
completed in the last year?
Yes
Athirdpartyassessmentwascompletedandasummaryoftheresultscanbemade
availableuponrequestunderNDA.
HLSY-05
Do you have policy and procedure, currently implemented, guiding how
security risks are mitigated until patches can be applied?
Yes
InalignmentwithFedRAMPModeraterequirements.
Vendor Answers Additional Information
HLDA-01
Does the environment provide for dedicated sin
g
le-tenant capabilities? If not,
describe how your product or environment separates data from different
customers
(
e.
g
.
,
lo
g
icall
y,
p
h
y
sicall
y,
sin
g
le tenanc
y,
multi-tenanc
y)
No
ArcGISOnlineutilizeslogicallyseparateproductionandnon‐production
environments(environmentisnotphysicallyseparate).SeparateSQLAzure
databasestostorehostedfeatureservicedataforeachcustomer'sArcGISOnline
HLDA-02
Is sensitive data encrypted, usin
g
secure protocols/al
g
orithms, in transport?
(
e.
g
. s
y
stem-to-client
)
Yes
ArcGISOnlineprovidesencryptionatRESTwithAES‐256,andencryptionintransit
withHTTPSviaTLS1.2.
HLDA-03
Is sensitive data encrypted, using secure protocols/algorithms, in storage?
(e.g. disk encryption, at-rest, files, and within a running database)
Yes
DataisencryptedatrestwithAES‐256whichisaFIPS140‐2compliantencryption
algorithms.ThisisinalignmentwithFedRAMPTailoredLowrequirements
HLDA-04
Are involatile backup copies made according to pre-defined schedules and
securely stored and protected?
Yes
Esridoesbackup
infrastructuredataandcustomerisresponsibleforbackupoftheir
dataatwhateverfrequencytheydesire.
DataisencryptedatrestwithAES‐256whichisaFIPS140‐2compliantencryption
algorithms.ThisisinalignmentwithFedRAMPTailoredLowrequirements
HLDA-05 Can the Institution extract a full or partial backup of data? Yes
Esriperformsbackupofinfrastructuredataandcustomeris
responsibleforbackup
oftheirdata
HLDA-06
Do you have a media handlin
g
process, that is documented and currently
implemented that meets established business needs and regulatory
requirements, including end-of-life, repurposing, and data sanitization
p
r
ocedu
r
es
?
Yes
AGOasaSaaSdoesnothandlephysicalmedia.ThisisaresponsibilityoftheCloud
infrastructureProvider(AWSandAzure)
HLDA-07
Does your staff (or third party) have access to Institutional data (e.g.,
financial, PHI or other sensitive information) within the application/system?
Yes
SelectEsrisystemadministraionstaffhavedirectaccesstocustomerdataandtheir
actionsfullylogged.Customerremainsresponsiblefortheirdataandmusthavetheir
own
policiesinplacetoavoidcopyingontoremovablemedia.
Thirdpartycloudproviderswillhavesystemsandproceduresinplacetopreventthis
copying,byrestrictingaccesstodatacentresandnotpermittingremovablemedia
withinthedatacentres.
Vendor Answers Additional Information
HLDC-01
Does your company mana
g
e the physical data center where the institution's
data will reside
?
No
ArcGISOnlineutilizedonlyAWSandMSAzuredatacenterslocatedwithintheUS,EU
orAsiaPacificregions.
HLDC-02
Are you
g
enerally able to accomodate storin
g
each institution's data within thei
r
g
eo
g
ra
p
hic re
g
ion?
Yes
ArcGISOnlinecustomerscanchoosetostoredataintheUS,EUorAsiaPacific
re
g
ions.
HLDC-03 Does the hosting provider have a SOC 2 Type 2 report available? Yes
SOC2reportsmaybeobtaineddirectlyfromAWSandMSAzure.
HLDC-04 Does your organization have physical security controls and policies in place? Yes
SeeCloudinfrastructureproviderdocumentationforphysicalsecuritycontrols
HLDC-05
Do you have physical access control and video surveillance to prevent/detect
unauthorized access to your data center?
Yes
Cloudinfrastructureproviderphysicalaccessisstrictlycontrolledbothatthe
perimeterandatbuildingingresspointsbyprofessionalsecuritystaffutilizingvideo
surveillance,intrusiondetectionsystems,and
otherelectronicmeans.Authorized
staffmustpasstwo‐factorauthenticationaminimumoftwotimestoaccess
datacenterfloors.Nosubcontractoraccessbe
y
ondcloud
p
roviders
Vendor Answers Additional Information
HLNT-01
Do you enforce network se
g
mentation between trusted and untrusted networks
(i.e., Internet, DMZ, Extranet, etc.)?
Yes
Thecloudinfrastructureprovidersutilizemultipleseparatenetworksegments.This
infrastructureprovidersegmentationhelpstoprovideseparationofcritical,back‐
endserversandstoragedevicesfromthepublic‐facinginterfaces.
FIDP-02
HLNT-02 Are you utilizing a stateful packet inspection (SPI) firewall? Yes
Cloudnativefirewallprotectionsareutilizedwhichprovidestatefulsecuritygroups.
Data
Datacenter
Networking
July 2023 Page 5

ARCGIS ONLINE HECVAT LITE V 3.04
HLNT-03 Do you use an automated IDS/IPS system to monitor for intrusions? Yes
CSP'shavetheirownIDS/IDP'sinplace.Anti‐virusdeployedtoadminsystemsaswell
asanysystemsconsumingexternalinformationsets.
HLNT-04 Are you employing any next-generation persistent threat (NGPT) monitoring? Yes
ArcGISOnlineutilizesnativecloudserviceprovidersnextgenthreatassessment
capabilities
HLNT-05
Do you require connectivity to the Institution's network for
support/administration or access into any existing systems for integration
p
ur
p
oses?
No
Vendor Answers Additional Information
HLIH-01 Do you have a formal incident response plan? Yes
Assessedbya3rdpartyannually.
HLIH-02
Do you have an incident response process and reportin
g
in place to investi
g
ate
an
y
p
otential incidents and re
p
ort actual incidents
?
Yes
IncidentmanagementisdelineatedwithinArcGISOnline'sIncidentResponsePlan
documentationaligningwithFedRAMPTailoredLowrequirements.
HLIH-03
Do you carry cyber-risk insurance to protect a
g
ainst unforeseen service
outa
g
es
,
data that is lost or stolen
,
and securit
y
incidents
?
Yes
Esrihascyberliabilityinsuranceandgeneralliabilityinsurancedetailscanbeshared
underNDA.
HLIH-04
Do you have either an internal incident response team or retain an external
team?
Yes
Internalincidentresponseteamisinplaceforbothproductsandcorporate
o
p
erations
HLIH-05 Do you have the capability to respond to incidents on a 24x7x365 basis? Yes
Cloudprovidershave24x7SOCsandEsrimonitorsforapplicationrelatiedissues.
Vendor Answers Additional Information
HLPP-01
Can you share the organization chart, mission statement, and policies for your
information security unit?
Yes
PleasereviewourTrustCenterhere:https://trust.arcgis.com/en/
PolicyTOCmaybesharedunderNDA.
SeeourArcGISSecurityDevelopmentLifecycledocumentation:
https://downloads.esri.com/RESOURCES/ENTERPRISEGIS/Esri_SDLC.pdf
HLPP-02 Are information security principles designed into the product lifecycle? Yes
SeeourArcGISSecurityDevelopmentLifecycledocumentation:
https://downloads.esri.com/RESOURCES/ENTERPRISEGIS/Esri_SDLC.pdf
HLPP-03 Do you have a documented information security policy? Yes
OurpolicyTableofContentsmaybesharedunderNDA.
Additional Information
HLTP-01
Will institution data be shared with or hosted by any third parties? (e.g. any
entity not wholly-owned by your company is considered a third-party)
Yes
ArcGISOnlineinfrastructureishostedinAWSandMSAzuredatacenterslocated
withintheUnitedStates
HLTP-02
Do you perform security assessments of third party companies with which you
share data? (i.e. hosting providers, cloud services, PaaS, IaaS, SaaS, etc.).
Yes
AthirdpartyassessmentsperformedanuallyaspartofFedRAMPrequirements.
HLTP-03 Do you have an implemented third party management strategy? Yes
Managementstrategyof3rdpartiesauditedforalignmentwithFedRAMP
requirementsannually.
HLTP-04
Do you have a process and implemented procedures for mana
g
in
g
your
hardware supply chain? (e.g., telecommunications equipment, export licensing,
com
p
utin
g
devices
)
Yes
Esridoes,butforAGO,sinceitisaSaaS,wedonothandlehardware.Thisismanaged
bytheCloudinfrastructureProvider
Policies, Procedures, and Processes
Third Party Assessment
Incident Handling
July 2023 Page 6
